Healthcare Data Breaches: A 20% Spike in 2026 and How to Respond
The digital age has brought unprecedented advancements to the healthcare sector, from electronic health records (EHRs) improving patient care coordination to telehealth expanding access to medical services. However, this digital transformation also comes with a significant dark side: an escalating threat landscape for cybersecurity. Recent reports indicate a staggering 20% increase in healthcare data breaches during the first three months of 2026 alone. This alarming statistic underscores a critical vulnerability within an industry responsible for safeguarding some of the most sensitive personal information imaginable. The repercussions of these breaches extend far beyond financial losses, impacting patient trust, operational continuity, and even the quality of care.
This article delves deep into the concerning rise of healthcare data breaches, exploring the underlying causes, the profound impacts on patients and providers, and, most importantly, outlining robust strategies to fortify cybersecurity defenses. Understanding the nature of these threats is the first step towards building a more resilient and secure healthcare ecosystem. As the industry continues its rapid digital evolution, the imperative to prioritize and invest in advanced cybersecurity measures has never been more urgent.
The Alarming Surge in Healthcare Data Breaches: A Q1 2026 Analysis
The beginning of 2026 has marked a concerning trend in the healthcare sector: a significant escalation in cybersecurity incidents. Data compiled from various cybersecurity firms and regulatory bodies reveals a 20% jump in reported healthcare data breaches compared to the previous quarter. This surge is not merely a statistical anomaly but a clear indicator of evolving and intensifying threats targeting healthcare organizations of all sizes, from large hospital systems to small private practices.
Several factors contribute to this sharp increase. Firstly, the sheer volume of sensitive data held by healthcare entities makes them an incredibly attractive target for cybercriminals. Patient records contain a treasure trove of personal information, including names, addresses, social security numbers, insurance details, and highly confidential medical histories. This data is invaluable on the dark web, where it can be used for identity theft, insurance fraud, and even blackmail.
Secondly, the rapid adoption of new technologies, often accelerated by the need for remote care and digital efficiency, has inadvertently expanded the attack surface. While telehealth platforms, cloud-based EHRs, and interconnected medical devices offer immense benefits, they also introduce new vulnerabilities if not secured meticulously. Many healthcare organizations, eager to innovate, may not have fully integrated robust security protocols into their expedited digital transformations.
Thirdly, the sophistication of cyberattack methods continues to advance. Ransomware attacks remain a pervasive threat, capable of crippling hospital operations and demanding exorbitant payments. Phishing campaigns are becoming more cunning, often impersonating trusted entities to trick employees into divulging credentials. Insider threats, both malicious and accidental, also play a significant role, highlighting the need for comprehensive employee training and access control.
Finally, a persistent challenge lies in the often-underfunded and understaffed IT security departments within healthcare. Many organizations struggle to keep pace with the rapidly evolving threat landscape due to budget constraints and a shortage of skilled cybersecurity professionals. This leaves them vulnerable to attacks that more robustly protected industries might deflect.
The 20% increase in healthcare data breaches in Q1 2026 serves as a stark warning. It signals that complacency is not an option and that a proactive, multi-layered approach to cybersecurity is no longer a luxury but an absolute necessity for every entity within the healthcare ecosystem. The urgency of this situation demands immediate and sustained attention from leadership, IT professionals, and every individual involved in handling patient data.
Understanding the Anatomy of a Healthcare Data Breach
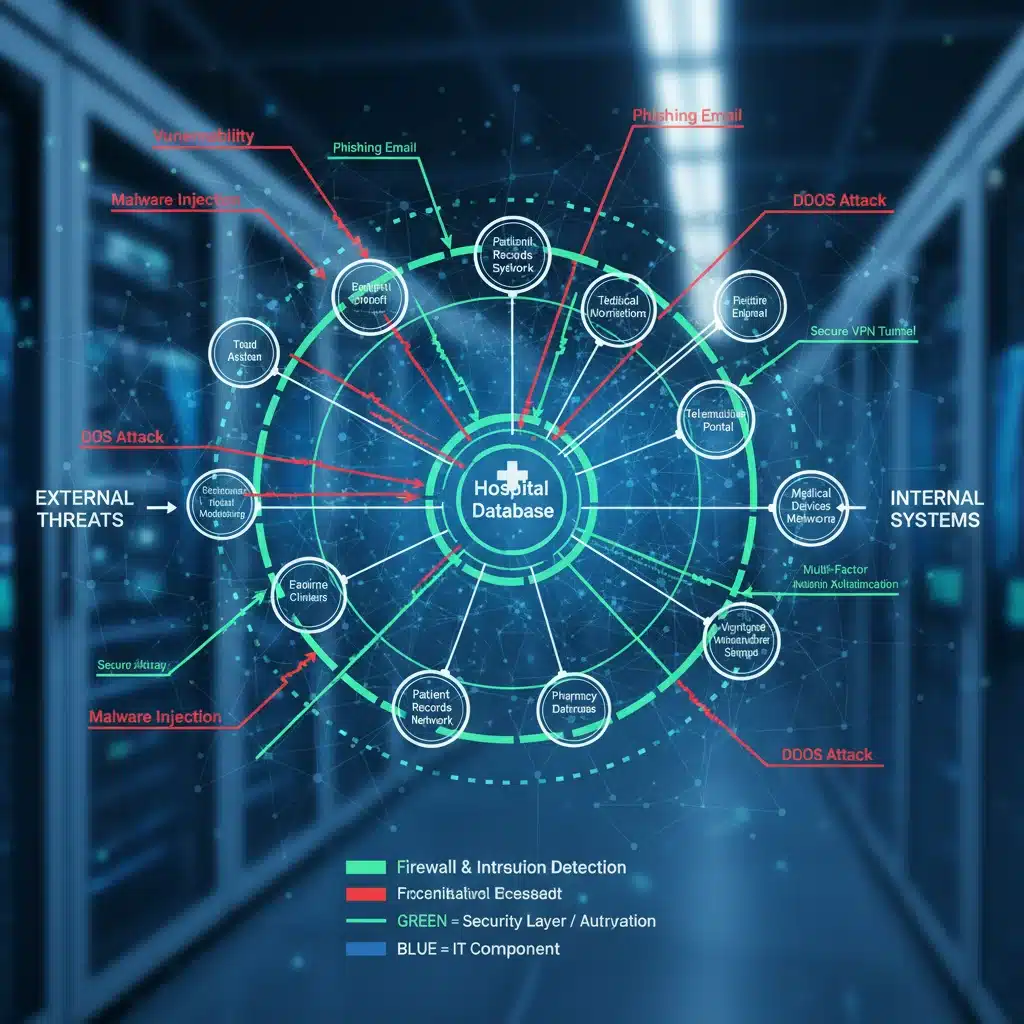
To effectively combat healthcare data breaches, it’s crucial to understand how they typically occur. While each incident has its unique characteristics, common attack vectors and vulnerabilities frequently emerge. By dissecting the anatomy of these breaches, healthcare organizations can better identify their weak points and implement targeted defenses.
Common Attack Vectors Exploited in Healthcare
- Phishing and Social Engineering: These are consistently among the most prevalent initial access methods. Attackers send deceptive emails, messages, or make phone calls designed to trick employees into revealing sensitive information, clicking malicious links, or downloading infected attachments. In healthcare, these often impersonate internal IT support, vendors, or even government agencies.
- Ransomware: This malicious software encrypts an organization’s data, rendering it inaccessible until a ransom is paid. Healthcare organizations are particularly susceptible due to the critical nature of patient data and the urgent need to restore access, making them more likely to pay.
- Exploitation of Software Vulnerabilities: Unpatched software, outdated operating systems, or misconfigured network devices create openings for attackers. Cybercriminals constantly scan for known vulnerabilities in commonly used healthcare systems and applications.
- Insider Threats: These can be either malicious (an employee intentionally stealing or exposing data) or accidental (an employee inadvertently causing a breach through negligence or error). Human error, such as misdelivery of patient information or improper disposal of records, remains a significant factor.
- Third-Party Vendor Breaches: Healthcare organizations often rely on numerous third-party vendors for services like billing, IT support, and data storage. If a vendor’s systems are compromised, patient data stored or processed by that vendor can be exposed, even if the primary healthcare entity’s systems are secure.
- Weak Authentication and Access Controls: Inadequate password policies, lack of multi-factor authentication (MFA), and excessive user privileges provide easy entry points for unauthorized individuals once credentials are stolen.
The Lifecycle of a Breach
A typical healthcare data breach often follows a predictable lifecycle:
- Reconnaissance: Attackers research their target, identifying vulnerabilities, employee email addresses, and potential entry points.
- Initial Compromise: Gaining initial access, often through phishing, exploiting a software vulnerability, or compromising a third-party vendor.
- Establish Foothold: Installing malware, creating new user accounts, or modifying existing configurations to maintain access.
- Privilege Escalation: Gaining higher-level access within the network to reach more sensitive systems and data.
- Internal Reconnaissance: Mapping the network, identifying critical data repositories, and understanding data flows.
- Lateral Movement: Moving across the network from the initial point of compromise to other systems containing valuable data.
- Data Exfiltration: Copying, transferring, or stealing the sensitive patient data.
- Covering Tracks: Deleting logs, removing malware, and generally attempting to hide their presence to avoid detection.
Understanding these stages allows organizations to implement security controls at each phase, from preventative measures during reconnaissance to detection and response capabilities during exfiltration. The complexity of modern healthcare IT environments means that a single point of failure can lead to widespread compromise, emphasizing the need for a holistic and layered security approach.
The Devastating Impact of Compromised Patient Data
The consequences of healthcare data breaches are multifaceted and severe, extending far beyond the immediate technical disruption. They inflict significant damage on patients, healthcare providers, and the industry as a whole. The 20% increase in breaches in Q1 2026 means a corresponding rise in these devastating impacts.
Impact on Patients
- Identity Theft and Financial Fraud: Patient data is highly valued by cybercriminals because it contains a wealth of information useful for identity theft, opening fraudulent credit accounts, or filing false tax returns. Medical identity theft can be particularly insidious, leading to incorrect medical bills, denial of genuine care, and misdiagnosis due to falsified medical records.
- Privacy Violations and Emotional Distress: The exposure of sensitive medical conditions, diagnoses, and treatment plans can cause immense emotional distress, embarrassment, and a profound sense of violation for patients. This can erode trust in their healthcare providers and the system designed to protect their most personal information.
- Disruption of Care: In the event of a ransomware attack, healthcare systems can be severely disrupted, leading to canceled appointments, delayed surgeries, and an inability to access critical patient records. This can directly impact patient safety and health outcomes, sometimes with life-threatening consequences.
- Increased Healthcare Costs: Patients may incur costs associated with identity theft protection services, credit monitoring, and resolving fraudulent medical claims, adding an unexpected financial burden.
Impact on Healthcare Providers and Organizations
- Financial Penalties and Legal Liabilities: Healthcare organizations face substantial fines for violating regulations like HIPAA (Health Insurance Portability and Accountability Act) in the United States, GDPR (General Data Protection Regulation) in Europe, and other regional data protection laws. These fines can run into millions of dollars. Additionally, organizations can be subject to costly lawsuits from affected patients.
- Reputational Damage and Loss of Trust: A data breach can severely tarnish an organization’s reputation, leading to a loss of patient trust and potentially a decline in patient enrollment. Rebuilding trust after a breach is a long and arduous process.
- Operational Disruption and Recovery Costs: The immediate aftermath of a breach involves significant operational disruption as systems are isolated, investigated, and restored. This often requires substantial investment in forensic analysis, incident response teams, and system upgrades, diverting resources from patient care.
- Loss of Intellectual Property and Research Data: Beyond patient records, healthcare organizations often hold valuable research data, proprietary drug formulations, or clinical trial results. Breaches can lead to the theft of this intellectual property, impacting competitive advantage and future innovation.
- Employee Morale and Productivity: Employees can experience increased stress and anxiety following a breach, impacting morale and productivity. They may also face increased scrutiny or blame, regardless of their direct involvement.
The collective weight of these impacts underscores the urgent need for robust cybersecurity measures. The 20% increase in healthcare data breaches is not just a statistic; it represents a growing threat to the well-being and privacy of millions, and a significant challenge to the sustainability and trustworthiness of the healthcare sector.
Fortifying Defenses: Essential Strategies for Cybersecurity in Healthcare
Given the escalating threat landscape and the critical nature of patient data, healthcare organizations must adopt a comprehensive, multi-layered approach to cybersecurity. Addressing the 20% surge in healthcare data breaches requires proactive measures, continuous vigilance, and a culture of security embedded throughout the organization. Here are essential strategies:
1. Robust Risk Assessments and Gap Analysis
- Regularly Assess Vulnerabilities: Conduct frequent penetration testing, vulnerability scanning, and security audits to identify weaknesses in systems, applications, and networks.
- Third-Party Risk Management: Evaluate the cybersecurity posture of all vendors and business associates who handle patient data. Ensure their security controls meet your organization’s standards and regulatory requirements.
- Data Mapping: Understand where sensitive data resides, how it flows through the organization, and who has access to it. This helps prioritize protection efforts.
2. Comprehensive Employee Training and Awareness
- Continuous Security Education: Implement ongoing cybersecurity awareness training for all staff, from clinicians to administrative personnel. This should cover phishing recognition, strong password practices, data handling protocols, and incident reporting procedures.
- Simulated Phishing Attacks: Regularly conduct simulated phishing exercises to test employee vigilance and provide immediate, targeted training to those who fall for the lures.
- Culture of Security: Foster an organizational culture where cybersecurity is everyone’s responsibility, encouraging employees to report suspicious activities without fear of reprisal.
3. Implementing Advanced Security Technologies
- Multi-Factor Authentication (MFA): Mandate MFA for all access to sensitive systems and patient data, significantly reducing the risk of compromised credentials.
- Endpoint Detection and Response (EDR)/Extended Detection and Response (XDR): Deploy advanced solutions that monitor endpoints for malicious activity, detect threats, and enable rapid response.
- Intrusion Detection/Prevention Systems (IDPS) and Firewalls: Utilize robust network security tools to monitor traffic, detect suspicious patterns, and block unauthorized access.
- Data Encryption: Encrypt sensitive data both at rest (on servers, databases, and backup media) and in transit (during transmission over networks).
- Secure Email Gateways: Implement solutions that filter out malicious emails, attachments, and links before they reach employee inboxes.
4. Strong Access Controls and Identity Management
- Principle of Least Privilege: Grant employees only the minimum access necessary to perform their job functions. Regularly review and update access permissions.
- Role-Based Access Control (RBAC): Implement RBAC to streamline access management and ensure consistency in permissions based on job roles.
- Centralized Identity Management: Use identity and access management (IAM) solutions to securely manage user identities and their access to various systems.
5. Incident Response and Business Continuity Planning
- Develop a Robust Incident Response Plan (IRP): Create a detailed plan outlining steps to detect, contain, eradicate, and recover from a cybersecurity incident. This plan should be regularly tested and updated.
- Regular Data Backups: Implement a comprehensive backup strategy, ensuring critical data is regularly backed up, encrypted, and stored offsite or in immutable storage, isolated from the primary network. Test these backups frequently to ensure data can be restored effectively.
- Business Continuity and Disaster Recovery (BCDR): Develop plans to maintain essential operations and quickly restore services in the event of a major cyberattack or other disaster.
6. Regular Patch Management and System Updates
- Timely Patching: Establish a rigorous process for applying security patches and updates to all operating systems, applications, and network devices as soon as they become available.
- Asset Inventory: Maintain an accurate and up-to-date inventory of all hardware and software assets to ensure no system is left unpatched.
By integrating these strategies, healthcare organizations can significantly enhance their resilience against the growing tide of healthcare data breaches. It’s an ongoing commitment that requires resources, expertise, and a proactive mindset, but the cost of inaction far outweighs the investment in robust security.
Regulatory Compliance and the Future of Healthcare Security
Navigating the complex landscape of regulatory compliance is a cornerstone of cybersecurity in healthcare. Regulations like HIPAA in the United States and GDPR in the European Union mandate stringent requirements for protecting patient data. The increasing frequency of healthcare data breaches, as evidenced by the 20% spike in Q1 2026, puts even greater pressure on organizations to not only meet but exceed these regulatory minimums.
HIPAA, GDPR, and Beyond
- HIPAA Compliance: The Health Insurance Portability and Accountability Act sets national standards for protecting sensitive patient health information. Its Security Rule specifically outlines administrative, physical, and technical safeguards that covered entities and business associates must implement. Non-compliance can lead to severe civil and criminal penalties.
- GDPR Compliance: For healthcare organizations operating within or serving residents of the European Union, the General Data Protection Regulation imposes even stricter data protection requirements, including principles of data minimization, privacy by design, and mandatory breach notification within 72 hours.
- State-Specific Regulations: Many U.S. states have their own data breach notification laws and additional privacy requirements that healthcare organizations must adhere to, adding layers of complexity.
- Emerging Regulations: The regulatory landscape is constantly evolving. Organizations must stay informed about new and impending privacy and security laws that could impact their operations.
Compliance is not merely about avoiding fines; it’s about establishing a baseline of security practices that protect patient trust and operational integrity. However, simply being compliant does not equate to being fully secure. Cybercriminals are not bound by regulations, and their tactics often evolve faster than legislative frameworks.
The Evolution of Healthcare Security: Predictive and Proactive
Looking ahead, the future of healthcare cybersecurity must shift from a reactive stance to a more predictive and proactive one. The current trend of escalating healthcare data breaches demands innovation and foresight.
- AI and Machine Learning for Threat Detection: Artificial intelligence and machine learning can analyze vast amounts of data to identify anomalous behavior and potential threats in real-time, often before they can cause significant damage. These technologies can learn from past attacks and adapt to new ones, offering a powerful layer of defense.
- Zero Trust Architecture: Moving away from the traditional perimeter-based security model, Zero Trust assumes no user or device, inside or outside the network, should be trusted by default. Every access request is verified, authenticated, and authorized, significantly reducing the impact of a breach if an attacker gains initial access.
- Cybersecurity Mesh Architecture: This approach decentralizes security, allowing for more flexible and scalable security policies that can be applied to individual assets, regardless of their location. It integrates disparate security services into a cohesive framework.
- Emphasis on Human-Centric Security: While technology is crucial, recognizing the human element as both a vulnerability and a strength is vital. Investing in user-friendly security tools, continuous education, and fostering a positive security culture will be paramount.
- Information Sharing and Collaboration: Healthcare organizations, often hesitant to share breach details due to reputational concerns, must increase collaboration and information sharing about threats and vulnerabilities. Collective intelligence can significantly enhance the industry’s overall defensive posture.
The 20% increase in healthcare data breaches in Q1 2026 is a wake-up call, signaling that existing measures are often insufficient. The future demands a commitment to continuous improvement, technological adoption, and a collaborative spirit to build a truly resilient and secure healthcare system.

Building a Resilient Healthcare Cybersecurity Framework
The alarming 20% surge in healthcare data breaches during the first three months of 2026 underscores an undeniable truth: cybersecurity is no longer an IT department’s concern alone, but a fundamental business imperative for every healthcare organization. The sensitive nature of patient data, coupled with the critical services healthcare provides, makes this sector an irresistible target for cybercriminals. The consequences of these breaches are not just financial; they can directly impact patient safety, erode public trust, and disrupt essential healthcare services.
To effectively counter these escalating threats, healthcare organizations must move beyond piecemeal solutions and embrace a holistic, adaptive, and continuously evolving cybersecurity framework. This framework should be built on several core pillars:
- Leadership Commitment: Cybersecurity must be championed from the top. Executive leadership needs to allocate adequate resources, establish clear policies, and foster a culture where security is integrated into every aspect of operations.
- Proactive Threat Intelligence: Instead of simply reacting to attacks, organizations must actively gather and analyze threat intelligence relevant to the healthcare sector. Understanding the latest attack vectors, malware strains, and adversary tactics allows for predictive defense strategies.
- Layered Security Architecture: A defense-in-depth approach is crucial. This involves implementing multiple layers of security controls – from network firewalls and intrusion detection systems to endpoint protection, data encryption, and robust access management – ensuring that if one layer fails, others are there to prevent a full compromise.
- Continuous Monitoring and Rapid Response: Security is not a set-it-and-forget-it endeavor. Continuous monitoring of systems, networks, and user activity is essential to detect anomalies and potential breaches early. A well-defined and frequently rehearsed incident response plan is critical for minimizing damage and ensuring swift recovery.
- Human Element as a Strength: While human error is often a vector for breaches, well-trained and security-aware employees are the first line of defense. Ongoing education, phishing simulations, and clear reporting mechanisms empower staff to be active participants in the organization’s security posture.
- Strategic Partnerships: Many healthcare organizations lack the in-house expertise to manage complex cybersecurity challenges. Partnering with specialized cybersecurity firms, threat intelligence providers, and managed security service providers (MSSPs) can augment internal capabilities and provide access to cutting-edge tools and expertise.
- Regular Review and Adaptation: The cybersecurity landscape is dynamic. Organizations must regularly review their security posture, adapt to new threats, update their technologies, and refine their policies and procedures to stay ahead of malicious actors.
The 20% increase in healthcare data breaches is a stark reminder that the battle for data security is ongoing and intensifying. However, by adopting a comprehensive and resilient cybersecurity framework, healthcare organizations can significantly enhance their ability to protect sensitive patient information, maintain operational continuity, and uphold the trust that is fundamental to the provision of quality healthcare. The time for decisive action is now, ensuring that the digital future of healthcare is secure, private, and trustworthy for all.






